Nowadays the Internet has turned into a brilliant place to pick up learning, trade thoughts, share data, make new companions and so forth. Have you ever seen your personal information in a public forum? Have you ever seen your personal information “grayed out”? If you have, know that it is not only cowardly but also illegal. There is a name for it: doxing.
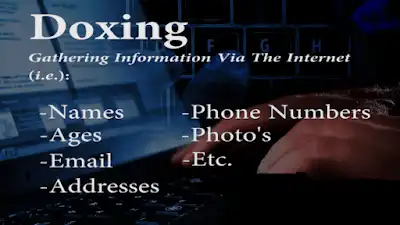
Doxing (spelling variant Doxxing) is an abbreviation of document tracing, the Internet-based practice of researching and publishing personally identifiable information about an individual. The methods employed in pursuit of this information range from searching publicly available databases and social media websites like Facebook to hacking and social engineering. It is closely related to cyber-vigilantism, hacktivism, and cyber-bullying.Doxware is a cryptovirology attack invented by Adam Young and further developed with Moti Yung that carries out doxing extortion via malware. It was first presented at West Point in 2003. The attack is rooted in game theory and was originally dubbed “non-zero sum games and survivable malware
What is Doxing?
Doxing is done by initially taking a piece of information (such as “name” or “email address”) and keeping it as a base to find out other possible details about the person. The term “doxing” is derived from the word “document tracing” which means to retrieve documents about a particular person or company in order to learn more about them.
Doxing Techniques:
Today, the Internet has grown to such a size that it contains almost any information that you’ve ever imagined! All you’ve to do is use the right techniques to search for what you want. Here is a list of doxing techniques that are most commonly used by Internet geeks and ethical hackers:
Social Networking Websites:
As most Internet users are found to be active on social media, social networking sites such as Facebook and LinkedIn provide a virtual goldmine of information necessary to perform doxing. As most users are unaware of online security issues, they have weak privacy settings on their profile. This makes it easy for the attackers to gain access to personal information such as photographs, real names, location, job, partner’s name etc.
Using Google:
Google is undoubtedly a powerful tool that plays a key role in doxing. Since Google indexes almost anything on the Internet (sometimes even the private information), it is possible to dox for details such as email ID, address, phone numbers and photographs of a person or company. Once you obtain the search results for your query, carefully examine the description part which in most cases contain the piece of information that you are looking for.
Whois Searches:
If a person or company has a website (or domain name) associated with them, you can easily perform a “whois search” for their website to obtain personal details such as full name, address, email, and phone number. there are a lot of websites available on the internet for whois lookup that will show up all the details associated with the domain name. Read more
Reverse Cell Phone Lookup:
A “Reverse Cell Phone Lookup” is simply a process of finding someone’s personal details such as name, age, address and related information by using their cell phone number and vice versa. There are many online services out there such as Intelius that provide access to the personal details about a given person based on his/her phone, name and email ID.
Why Would Anyone Want to Perform Doxing?
Most people perform doxing out of general curiosity about a person or company. However, there are some wicked minds out there who do this for the purpose of blackmailing or taking revenge by exposing the information that they have gathered about the person.
What are the Consequences of Doxing?
It can be slightly irritating and embarrassing when private data fall into the hands of people who are not intended to have access to such information. However, things can go even worse if the doxed information such as a person’s social activities, medical history, sexual preference and other vital bits of information is made public. This can have a serious threat to health, livelihood or relationship of the victim.
Steps to Protect Yourself from Doxing:
The following are some of the most commonly targeted pieces of information that can be easily obtained through doxing:
- Full name
- Age, gender, and date of birth
- Location and place of birth
- Email addresses and username
- Phone number
- Social networking profiles, websites, and blogs
So, it is always a good practice to keep the above bits of information hidden. Even though it is not possible to do this in all cases, you can still take care to protect as much information as you can from going public. You can consider the following additional tips for further protection:
Do not upload personal photographs on web albums such as “Picasa”. Even if you do, make sure that your album is hidden from public and search engines.
If you do not intend to show up your profile on search engines, it is a wise choice to make all the Internet profiles private.
Maximize the privacy settings of your social network profiles. Make sure that your individual albums and photographs have their privacy settings configured.
Do not use the same email address for all your accounts. Instead, create separate email IDs for individual activities such as gaming, forum participation, banking accounts etc.
Is Doxing a Crime?
Doxing is definitely not a crime when used to the ethical standards and no harm is being caused to anyone. However, if doxing is done to cause intentional damage such as harassment, blackmailing or taking revenge it might well be considered an offense.